Project Overview
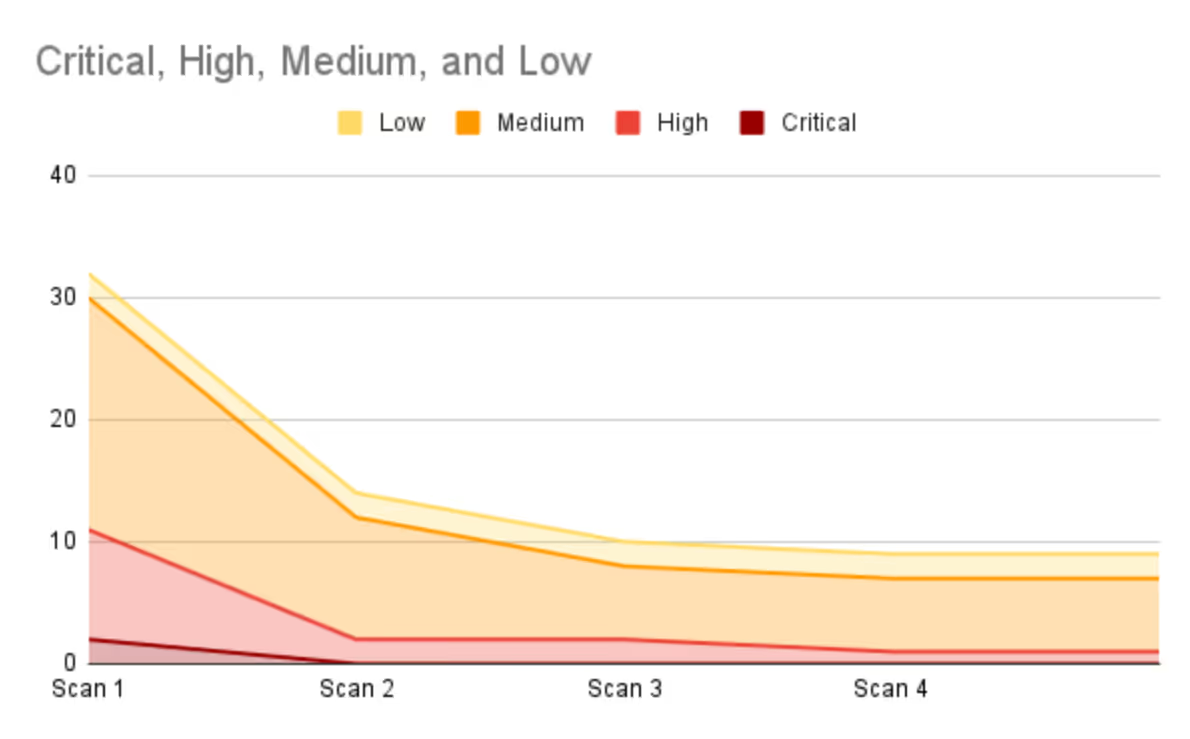
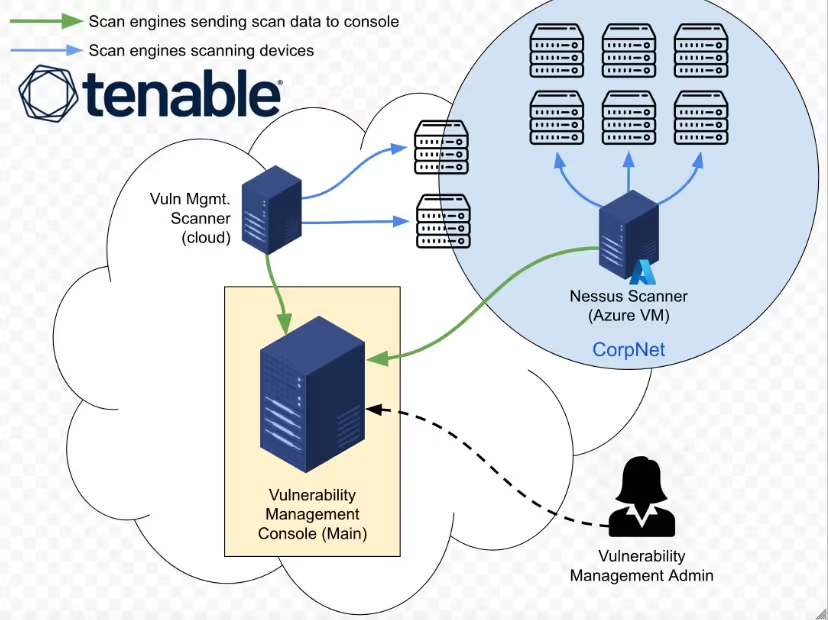
In this project, we simulate the implementation of a comprehensive vulnerability management program, from inception to completion.
Inception State: the organization has no existing policy or vulnerability management practices in place.
Completion State: a formal policy is enacted, stakeholder buy-in is secured, and a full cycle of organization-wide vulnerability remediation is successfully completed.
Technology Utilized
- Tenable (enterprise vulnerability management platform)
- Azure Virtual Machines (Nessus scan engine + scanned target)
- PowerShell & BASH (remediation scripts)
Step 1. Vulnerability Management Policy Draft Creation
This phase focuses on drafting a Vulnerability Management Policy as a starting point for stakeholder engagement. The initial draft outlines scope, responsibilities, and remediation timelines, and may be adjusted based on feedback from relevant departments to ensure practical implementation before final approval by upper management.
1. Policy Overview
This policy establishes the framework for managing vulnerabilities within LogN Pacific's IT infrastructure to ensure the security and integrity of our systems through timely and effective identification, evaluation, and remediation of threats.
2. Scope
This policy applies to all IT assets owned or operated by LogN Pacific, including networks, servers, endpoints, and associated applications.
3. Responsibilities
Chief Information Security Officer (CISO): Oversight of the vulnerability management process and ensuring compliance with this policy. Department Heads: Responsible for ensuring compliance within their respective departments.
Chief Information Officer (CIO): Ensuring that vulnerability management is integrated with LogN Pacific's overall IT strategy.
4. Vulnerability Scan Schedule
Routine Scans: Conduct monthly scans of all IT assets to identify vulnerabilities.
Ad-Hoc Scans: Perform scans in response to significant security alerts or when new vulnerabilities are reported.
A local agent will be used for vulnerability assessment on end-user workstations
5. Remediation Schedule and Cadence
Based on the Common Vulnerability Scoring System (CVSS):
Critical RCE ZERO DAY (CVSS 9.0-10): Remediate or mitigate within 48 hours.
Critical (CVSS 9.0-10): Remediate or mitigate within 48 hours.
High (CVSS 7.0-8.9): Remediate or mitigate within 7 days.
Medium (CVSS 4.0-6.9): Remediate or mitigate within 30 days.
Low (CVSS 0.1-3.9): Remediate or mitigate within 90 days.
6. Maintenance Plans
Routine Patching: Apply security patches and updates on a scheduled monthly basis.
Emergency Patching: Initiate within 24 hours for critical vulnerabilities that pose immediate risks.
Emergency Mitigation: Implement temporary measures (e.g., firewall rules, access restrictions) to protect against vulnerabilities while permanent solutions are developed.
Unpatchable Assets: Implement segmentation, increased monitoring, or phased removal from the environment.
7. Non-Compliance Consequences
Departments failing to comply with this policy will face:
Immediate review of their procedures.
Mandatory retraining for involved personnel.
Escalation to senior management for further disciplinary actions including termination
8. Sign-Off
Chief Information Security Officer (CISO)
Sign: Mike Smith
Date: 20 August 2025
Chief Information Officer (CIO)
Sign: Jane Doe
Date:20 August 2025
Chief Executive Officer (CEO)
Sign: Bob Roberts
Date:20 August 2025
9. Review and Revision
This policy will be reviewed annually or sooner if necessary to accommodate changes in business processes or to address emerging threats.
Document Control
Version: 1.1
Date: 20 Aug 2025
Author: Tyler D.
Step 2. Mock Meeting: Policy Buy-In (Stakeholders)
In this phase, a meeting with the server team introduces the draft Vulnerability Management Policy and assesses their capability to meet remediation timelines. Feedback leads to adjustments, like extending the critical remediation window from 48 hours to one week, ensuring collaborative implementation.
Vulnerability Management Policy Buy‑In
Manager: Thanks for reviewing the draft policy. Any concerns?
Team Lead: The 48‑hour remediation window for all critical vulnerabilities isn’t realistic with current staffing.
Manager: Understood. Let’s set the window to one week, and reserve the 48‑hour requirement for zero‑day or high‑risk cases.
Team Lead: That works. Could we also have some flexibility during the rollout?
Manager: Yes. Departments will have a six‑month adjustment period before full enforcement.
Team Lead: Fair enough. We appreciate being included in the process.
Manager: Of course. Collaboration is key. Thanks for your input.
Step 3. Policy Finalization & Senior Leadership Sign-Off
After gathering feedback from the server team, the policy is revised, addressing aggressive remediation timelines. With final approval from upper management, the policy now guides the program, ensuring compliance and reference for pushback resolution.
1. Policy Overview
This policy establishes the framework for managing vulnerabilities within LogN Pacific's IT infrastructure to ensure the security and integrity of our systems through timely and effective identification, evaluation, and remediation of threats.
2. Scope
This policy applies to all IT assets owned or operated by LogN Pacific, including networks, servers, endpoints, and associated applications.
3. Responsibilities
Chief Information Security Officer (CISO): Oversight of the vulnerability management process and ensuring compliance with this policy.Department Heads: Responsible for ensuring compliance within their respective departments.
Chief Information Officer (CIO): Ensuring that vulnerability management is integrated with LogN Pacific's overall IT strategy.
4. Vulnerability Scan Schedule
Routine Scans: Conduct monthly scans of all IT assets to identify vulnerabilities.
Ad-Hoc Scans: Perform scans in response to significant security alerts or when new vulnerabilities are reported.
A local agent will be used for vulnerability assessment on end-user workstations
5. Remediation Schedule and Cadence
Based on the Common Vulnerability Scoring System (CVSS):
Critical RCE ZERO DAY (CVSS 9.0-10): Remediate or mitigate within 48 hours.
Critical (CVSS 9.0-10): Remediate or mitigate within 7 days.
High (CVSS 7.0-8.9): Remediate or mitigate within 2 weeks.
Medium (CVSS 4.0-6.9): Remediate or mitigate within 30 days.
Low (CVSS 0.1-3.9): Remediate or mitigate within 90 days.
6. Maintenance Plans
Routine Patching: Apply security patches and updates on a scheduled monthly basis.
Emergency Patching: Initiate within 24 hours for critical vulnerabilities that pose immediate risks.
Emergency Mitigation: Implement temporary measures (e.g., firewall rules, access restrictions) to protect against vulnerabilities while permanent solutions are developed.
Unpatchable Assets: Implement segmentation, increased monitoring, or phased removal from the environment.
7. Non-Compliance Consequences
Departments failing to comply with this policy will face:
Immediate review of their procedures.
Mandatory retraining for involved personnel.
Escalation to senior management for further disciplinary actions including termination
8. Sign-Off
Chief Information Security Officer (CISO)
Sign: Mike Smith
Date: 20 August 2025
Chief Information Officer (CIO)
Sign: Jane Doe
Date:20 August 2025
Chief Executive Officer (CEO)
Sign: Bob Roberts
Date:20 August 2025
9. Review and Revision
This policy will be reviewed annually or sooner if necessary to accommodate changes in business processes or to address emerging threats.
Document Control
Version: 1.2
Date: 20 Aug 2025
Author: Tyler D.
Step 4. Mock Meeting: Initial Scan Permission (Server Team)
The team collaborates with the server team to initiate scheduled credential scans. A compromise is reached to scan a single server first, monitoring resource impact, and using just-in-time Active Directory credentials for secure, controlled access.
Security Analyst: Good morning. Now that our vulnerability management policy is in place, I’d like to begin scheduling credentialed scans of your environment.
IT Manager: Sounds good. What’s involved, and how can we help?
Security Analyst: We’re planning weekly scans of the server infrastructure. It should take about 4–6 hours to cover all ~200 assets. We’ll need administrative credentials so the scan engine can log in and perform deeper checks.
IT Manager: Hold on—what exactly does scanning entail? I’m concerned about resource utilization, and granting admin credentials to every machine doesn’t sound safe.
Security Analyst: Valid concerns. The scan engine sends controlled traffic to identify vulnerabilities—checking registry entries, outdated software, and insecure protocols. Credentials are required for that deeper visibility.
IT Manager: As long as it doesn’t impact server availability, we can proceed.
Security Analyst: To be cautious, let’s start with a single server and monitor resource usage.
IT Manager: That’s reasonable. For credentials, could we use Active Directory accounts that remain disabled until scans are run, then deprovisioned afterward?
Security Analyst: Exactly—just‑in‑time access. That approach works well.
IT Manager: Great. I’ll have the team set up the automation for account provisioning.
Security Analyst: Perfect. I’ll follow up once the credentials are ready. Thanks for the collaboration.
IT Manager: Sounds good. Talk soon.
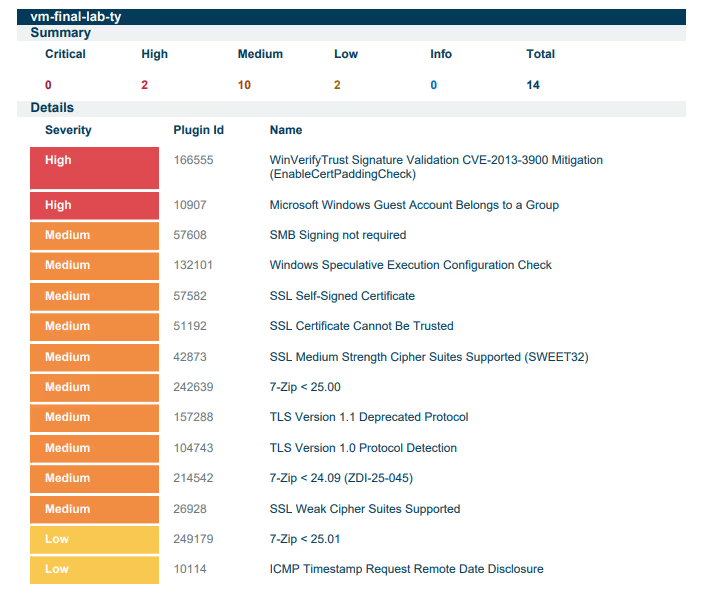
Step 5. Initial Scan of Server Team Assets
In this phase, an insecure Windows Server is provisioned to simulate the server team's environment. After creating vulnerabilities, an authenticated scan is performed, and the results are exported for future remediation steps.

Step 6. Vulnerability Assessment & Priorization
We assessed vulnerabilities and established a remediation prioritization strategy based on ease of remediation and impact. The following priorities were set:
1) Third Party Software Removal (Wireshark)
2) Windows OS Secure Configuration (Protocols & Ciphers)
3) Windows OS Secure Configuration (Guest Account Group Membership)
4) Windows OS Updates
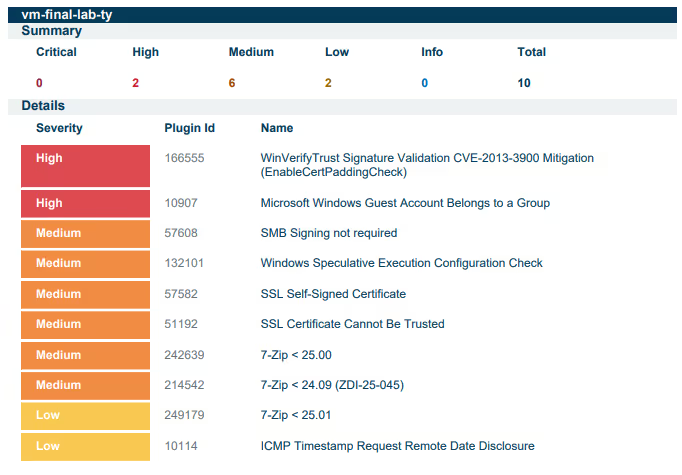
Step 7. Distributing Remediations to Remediation Teams
The server team received remediation scripts and scan reports to address key vulnerabilities. This streamlined their efforts and prepared them for a follow-up review.


%201.svg)